What's new with State Privacy Laws?
There are now ten comprehensive privacy laws enacted in the United States. The new 2023 laws include those in Montana, Indiana, Iowa, Tennessee, and Texas. These laws join existing laws, including California, Utah, Colorado, Virginia, and Connecticut. These laws all share commonalities that resemble the EU's Global Data Protection Regulation (GDPR). However, the recently passed law in Tennessee stands out from all other laws in one significant way.
We spoke with Jerrod Montoya, an attorney and expert in managing privacy risk, about how healthcare technology vendors can manage risk in the face of the rapidly evolving landscape of information privacy legislation.
Q: Given that risk management is poorly defined in the law and most, if not all of the new privacy laws are yet to be litigated. How do corporate leaders at healthcare technology companies know they have the correct processes in place?
“The challenge for any leader is to understand what is going on in the industry, especially when a situation arises where you have rapidly expanding laws and rapidly changing data privacy laws. There's a tendency in the health tech sector to think well, if we're dealing with data privacy, it's only HIPAA, and HIPAA does not apply to me. The reality is the landscape has changed a lot recently.”
“For example, under the breach notification rule, the FTC is taking enforcement actions for deceptive practices based on handling of personal information. More importantly, state laws have evolved to a point where they're filling a gap that previously existed. So even if HIPAA doesn’t apply, the state privacy laws like CCPA do."
“Combine that with the fact that health information is still very valuable on the black market. So, for health tech leaders, if you haven't looked at this within the last year or six months, you're probably behind.”
Q: If I'm the general manager of a division or maybe the CEO of a health tech startup and I'm aware I need to be complying with the laws. Maybe I'm not a lawyer nor a technologist. How do I know what to tell someone to do? And how do I get that piece of mind to know that I'm properly covered?
“Peace of mind comes from understanding your risk environment. What is the business risk surrounding sensitive data? If you're not getting that, it’s a red flag. You should look at continuous monitoring of your program as a whole. What are the issues and the deficiencies that are being found and are they being resolved? The reality is I think you have to understand your business process first, understand the risk that's being posed by the handling and processing of sensitive information that you have, and then look at the case law as well.” 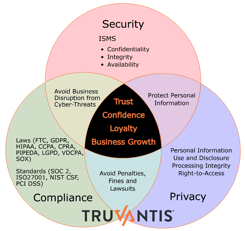
“More recently, there has been a trend pointing towards using common frameworks, which is an evolving area. For example, there is an existing framework from the National Institute of Standards and Technology (NIST). NIST has a privacy framework that works alongside the cybersecurity framework and that is one option is to benchmark the framework maturity of the processes in place. Or you can look at other common frameworks that are more ubiquitous in the information security space. For example, CIS controls, ISO27x, NIST 853, and SOC 2. These are other tools you can leverage to get assurance that you have solid practices around protecting sensitive information.”
“From a legal standpoint, look at what the FTC is doing. For example, in the case of Flo Health, Inc. and GoodRx. Notice how they’re approaching these health tech companies and what they're requiring them to do. You can see if there are any parallels to how your business is operating and learn from those cases and business practices as examples of how well you're doing or how significant the risk is to your organization.”
Q: Below the board of directors, who in an enterprise should be accountable for information, privacy, policies and practices?
“The fact is you should have somebody. If you're capable of having a designated role in, say, a Chief Privacy Officer or other privacy-specific position, that's ideal. There is a lot of legal cross-over. So having a GC or a legal component, no matter where it's housed, is very important. I think the key at the end of the day is that there are some key pillars to data protection and data privacy that you need when making decisions wherever it comes from. You could also outsource that role to a consulting organization like Truvantis.”
![]() Jerrod Montoya, JD, CIPP/US
Jerrod Montoya, JD, CIPP/US
Jerrod Montoya is an attorney and expert in privacy, governance risk and compliance. He is a business-oriented practitioner with a unique blend of legal, information security and privacy experience who aids organizations with the implementation of intelligent solutions to meet business objectives.
Let the Truvantis vCISO Service Manage Your Comprehensive Security & Privacy Program
Many organizations trust Truvantis, including banks, financial services, state and local government, airports, retail, healthcare & health-tech organizations, public companies, startups, large nonprofits and major sports teams.
We don't believe in one-size-fits-all security. Instead, we will create a customized program tailored to your business requirements. Our mission is to help you build practical & effective cybersecurity, privacy & compliance programs that balance budget and risk.
“We’re thrilled with the vCISO services we’ve received from Truvantis. Technical and compliance expertise is always accompanied by practical advice. I’d trust our Truvantis professional to handle anything on behalf of our company.”
- Sarah Bimber JD, MPH, General Counsel, Amino
Truvantis offers comprehensive expertise in implementing, testing, auditing, and operating information security, privacy & compliance programs. We've helped organizations of all sizes improve their cybersecurity posture through practical, effective, and actionable programs—balancing security, technology, business impact and organizational risk appetite.
Listen to the Full Interview
For the full interview please visit The Truvantis Risk Radar YouTube channel or listen to the podcast.
Resources:
- Flo Health, Inc.
- FTC Enforcement Action to Bar GoodRx from Sharing Consumers’ Sensitive Health Info for Advertising
About Truvantis
Not every business can internally support the staffing and resources necessary for developing robust incident response programs on its own. Fortunately, you can partially or fully outsource the job of building in, training the team and running the tabletop exercises to trusted partners. At Truvantis, our vCISO service is not a one-size-fits-all solution. We take a personalized approach to your business situation, cybersecurity, privacy and incident response requirements.
Truvantis is a cybersecurity consulting organization providing best-in-class cybersecurity services to secure your organization's infrastructure, data, operations and products. We specialize in helping our clients improve their cybersecurity posture by implementing testing, auditing and operating information security programs.


.png)





.png)
